Technology
Hacknowledge Technology
- Custom solution to secure your network
- Easy integration with your existing technology
- Sensor + IDS + SIEM + sandboxing/file analysis
- On-premise, cloud, or hybrid
- Easy to implement
VISION Cyber ManagementTM by HACKNOWLEDGE is a fully integrated cybersecurity monitor and response solution comprised of our cutting-edge sensor, IDS, SIEM, and sandbox technology working in conjunction with our enterprise-level Managed Detection and Response (MDR) services.
Intrusion Detection System (IDs)
Hacknowledge IDS merges analysis with threat intelligence. Our security team continuously updates the IDS solution with the latest threat intelligence, protecting your network from emerging threats.
- Monitor your network for malicious activities or policy violations
- Detect threats as they emerge in the cloud and on premises
- Monitor AWS and Azure for your public cloud environments
- Collect and correlate events from your existing IDS into a single console
- Comprehensive intrusion detection as part of an all-in-one security management console
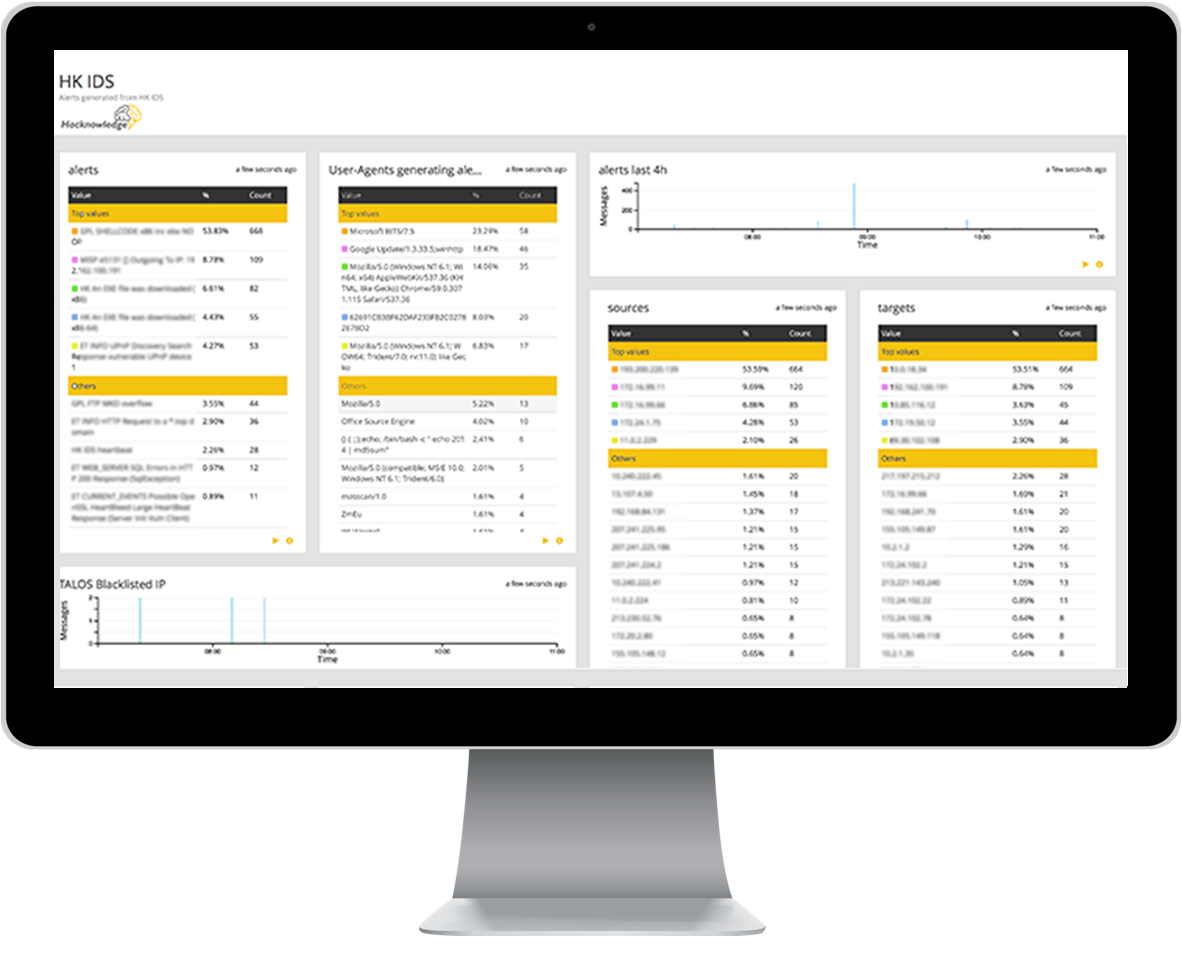

Security Information & Event Management (SIEM)
Hacknowledge SIEM collects, normalizes, and correlates your logs to help you effectively detect and respond to emerging threats. We apply threat intelligence, expert rules, workflows, and proprietary processes to drive investigation.
Our team will help create and maintain SIEM correlation rules. Our advanced data analytics and built-in intelligence enables us to: Reduce log data noise, quickly assess the risk of an event, and escalate alerts as that risk grows. It provides a holistic view of your network and helps you detect and respond to emerging threats.
Vision Sensor
Our custom sensors are developed to provide visibility to your network. They are scalable and as many sensors required can be added in order to provide a holistic view of your network in real time. Our custom sensors also bring in security features such as IDS, vulnerability scanning, honeypot, file analysis, and more. If you already have those technologies, our sensors will work in conjunction with what you already have. If you don’t, you can leverage our technology for additional visibility and security coverage.
Instead of relying only on log-correlation, our sensors generate strong Indicators of Compromise (IOC) that enable us to be far more effective in detecting security breaches while reducing costs. Deployed as either hardware or software, we developed our sensors with built-in intelligence that allows our sensors to filter and prioritize the data reducing alerts that are not of value. Our custom sensors are scalable and can be deployed on-premise, in the cloud, or in hybrid installations.

Hardware Sensors
Recommended For Subnets & Branch Offices
Plug and play – setup in minutes
Scalable (via additional sensors)
Up to 10 network interfaces
Speed up to 40Gbps
Virtual Sensors
Recommended For Virtual & Core Networks
Fully managed by Hacknowledge
Scalable (via additional sensors)
VMWare, Xen, HyperV
Speed up to 40Gbps
Sensor Features
Integrated Detection & Analysis Modules
Log collector / parser / caching
IDS / file analysis
Honeypots / canaries
Vulnerability scanner
An all-inclusive, fully integrated Hacknowledge proprietary solution with world-class event monitoring at its core.
Vision Cyber ManagementTM
a HACKNOWLEDGE Cutting-Edge Solution
Sandboxing / File Analysis
Our Sandboxing and File Analysis technology will help you detect malicious content that threatens your network. These threats can be from any source, including online file sharing, portable file storage devices, and files from outside your network.
We help you detect and respond to cyberattacks by automatically scanning file content for signs of malicious threats. Additionally, our Sandbox can be used as a malware analysis tool where your IT team can send suspicious files to be analyzed. Our sandbox solution is fully Integrated with our products making it easy to manage, maintain, and apply threat intelligence.
Threat / Intelligence
Armed with intelligence about how and why you are being targeted, as well as by whom, your team can better mitigate threats and build a proactive defense strategy. Hacknowledge monitors specific websites 24/7 to gather intelligence and information about potential attacks.
Our security experts analyze and prioritize both global and targeted threats with a proactive approach in responding to potential attacks. We review thousands of threat information data points daily to identify vulnerabilities that may introduce risk into your organization’s network. We develop countermeasures and add new rules into our IDS and SIEM, so you don’t have to.
- Monitoring your exposure in publicly available data online to help you assess potential threats
- IDS linked to 24/7 collection of intelligence via monitoring of specific sources online
- Detecting and monitoring activities from known malicious attackers
- Daily contextual adaptation of custom rules and signatures from intelligence gained
Vulnerability / Scan
Hacknowledge offers vulnerability scanning to help you gain insight into your network security risks, then provide professional advice to help you with remediation efforts. Our sensors can run vulnerability scans that will help prepare your threat reports and tune the IDS. Gain actionable insight with our FREE UNLIMITED vulnerability scanning technology.
Features & Benefits
- Distributed attack detection
- Encrypted and compressed event data
- Log monitoring from a single point
- Canaries to detect leakage of sensitive files
- Advanced blacklist management capabilities
- Cyber threat detection interface
- Centralized log retention in the cloud
- Honeypots to trap hackers
- Scalable architecture
- Near real-time malicious activity detection
- Cloud environment data collection
- Detecting use of known hacking tools
- Real-time threat intelligence support
- Real-time geographic awareness map
- Centralized IDS configuration / management

Splunk / Professional Services
Our highly Certified Splunk Engineers enable organizations to gain real-time operational intelligence by harnessing the value of their data. Splunk Enterprise collects and indexes data at massive scale, regardless of format or source, and enables users to quickly and easily search, correlate, analyze, monitor and report on this data. Splunk Enterprise is designed to help users in various roles, including IT, security teams and business professionals, to quickly analyze machine data and realize real-time visibility into and intelligence about their organization’s operations.




Microsoft / Azure Sentinel
Our Certified Azure Security Engineers (AZ-500) manage its implementation, configuration and tuning. Azure Sentinel can be integrated with our MDR solution to provide a 24×7 Monitoring service with our security analysts.